Complete Guide to Safe Crypto Storage
Before we talk about how to securely store cryptocurrency, let’s talk for a moment about what exactly needs to be protected. A cryptocurrency wallet does not actually store cryptocurrency; the cryptocurrency always stays on the blockchain. Rather, a crypto wallet stores and protects private keys. Private keys are strings of randomly generated characters that “unlock” coins and allow them be spent. When you buy cryptocurrency, you are actually buying private keys that allow you to use the cryptocurrency associated with that key.
Some wallets allow their users to maintain control over the keys; others (ie Coinbase or Bittrex) keep the keys safe and encrypted, but do not provide users with access to them. Know this: she who holds the private keys controls the coins, end of story. If you choose to use a wallet that holds your private keys for you, be absolutely sure that the wallet has a stellar reputation.
Public Keys and Private Keys
The relationship between public and private keys can also be explained with a metaphor. Imagine a public mailbox. The mailbox is your public key–anyone can put letters (cryptocurrency) into the mailbox, but only the mailman, with their key (you with your private key) can open the box and take the letters out. If someone else has your private key, they can steal your letters (cryptocurrency) from your mailbox (wallet).
Private keys are essentially the “signatures” that authenticate any transaction on a blockchain; the private key is used to confirm that a transaction has come from a user, and keeps a transaction from being tampered with after it has been issued.
Public keys can be shared with anyone, as they can be used to send cryptocurrency to you. You can share your public keys as much as you like. Public keys are cryptographically derived from your coins’ private keys, but they are so heavily encrypted that it would take even the most powerful supercomputer billions of years (204 tresvigintillion, to be exact) to crack the code.
Wallet Addresses
Your crypto wallet address is not the same as a public key, although they are mathematically related (the wallet address is derived from the public key). Your wallet address is a “hashed” version of your public key. “Hashing” is the process of transforming a string of characters into a smaller, encrypted version of itself. For example, a Bitcoin’s public key is 256 bits, while a wallet’s public address is 160 bits.
IMPORTANT: When you are creating or using any kind of cryptocurrency wallet, know that the wallet you are using MUST be compatible with the cryptocurrency you are attempting to store in it. Attempting to send the wrong kind of cryptocurrency into the wrong kind of wallet (ie, sending ETH to a BTC wallet) could result in the permanent loss of your funds.
Hardware Wallets
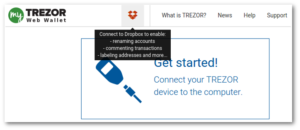 If you have the funds to spare, investing in a hardware wallet is probably the best way to keep your coins safe. KeepKey, Ledger, and Trezor all offer hardware wallets that are easy-to-use, and a must-have for people who plan on holding larger investments in crypto. The coins and software wallets your hardware wallet is compatible with will depend on the wallet itself. For example, the Trezor wallet has its own software interface (MyTrezor) and is compatible with several other software wallets, including Electrum.
If you have the funds to spare, investing in a hardware wallet is probably the best way to keep your coins safe. KeepKey, Ledger, and Trezor all offer hardware wallets that are easy-to-use, and a must-have for people who plan on holding larger investments in crypto. The coins and software wallets your hardware wallet is compatible with will depend on the wallet itself. For example, the Trezor wallet has its own software interface (MyTrezor) and is compatible with several other software wallets, including Electrum.
All of these wallets provide users with the option of creating a backup, so if your hardware wallet is lost or destroyed, never you fear–it can be recovered. While there are some white-hat hackers that have found a few vulnerabilities across hardware wallet technology, this method of storing your crypto is very safe, and worth the investment.
Paper Wallets: Cheap Cold Storage
There are lots of services that offer paper wallet creation online–Bitcoin.com, MyEtherWallet, and WalletGenerator.net, to name a few.
The more offline you can be when creating a paper wallet, the more secure your wallet will be. Some services, like WalletGenerator.net, have a downloadable zip file that will run the wallet generator offline. In fact, WalletGenerator recommends that you unplug your Internet router completely during the creation of your wallet. If you must be online when creating your paper wallet, be sure to use an encrypted browser, like Epic.
Once your wallet is created, and your cryptocurrency has been stored in it, print several copies of your wallet and spread the copies between several secure places. Never let anyone see your private keys, even for a few seconds. There was a famous instance Matt Miller momentarily flashed his private key on live television during a broadcast on how to give a Bitcoin for Christmas. Within seconds, his Bitcoins were removed from his wallet–however, the thief offered them back with a slap on the wrist.
Well, for starters, a paper wallet is made of paper, and is therefore vulnerable to all the things that paper is vulnerable–fire, water, insects, and a host of other physical threats. Therefore, it’s a good idea to laminate your paper wallet and to make multiple copies that are stored in different places.
It’s also very important to use a printer that is not connected to the internet when printing your paper wallet. The “internet of things” is still in its early stages, and is more vulnerable to attack–that crockpot on your kitchen counter that you can program at work may allow a hacker to get into your network. Printers connected to the internet may also be hacked, and your information can be stolen.
Software Wallets: Choosing the Right One
Software wallets are by and large the most commonly used kinds of wallets in the world of crypto. When you’re looking for a software wallet, there are a few things to take into consideration:
What kind of accessibility do you need?
Are you searching for a wallet that is accessible from your smartphone, online, or desktop?
What kind of backup options does the wallet offer?
Do you want a wallet that allows you to be in control of your private keys, or a wallet that keeps your private keys for you?
What kind of reputation does the wallet have?
What kind of customer service is available? (This question is particularly important for wallets that keep control of their users’ private keys.)
For a comprehensive review on ten of the most popular wallets, check out our “Ten Best Software Wallets” post.
Storing Altcoins: How to Find and Choose the Right Wallet
 When it comes to some of the newer altcoins, it can be tricky to find a wallet that will store them. However, it is unwise to leave your altcoins on the exchange where you bought them, as exchanges are particularly vulnerable places.
When it comes to some of the newer altcoins, it can be tricky to find a wallet that will store them. However, it is unwise to leave your altcoins on the exchange where you bought them, as exchanges are particularly vulnerable places.
The first place to look for a wallet that will hold your altcoin is that coin’s official website. Make sure that the wallet you are downloading is officially affiliated with the coin–unfortunately, there are dishonest people on the internet who create fake wallets that will give them access to your private keys, allowing them to steal your coins. Be safe, and only download wallets from secure, verified sources.
If your altcoin does not yet have its own wallet, check some of the more reputable altcoin wallets–Coinomi, Jaxx, Exodus, and MyEtherWallet may be able to cover your needs. All of these wallets allow you to have control over your private keys.
If you must leave your altcoins on an exchange for a short time, be sure to take full advantage of that particular exchange’s security measures. Reputable exchanges, like Bittrex and Gemini, offer two-factor authentication that can help keep your coins safe.
Backing Up Your Wallet
There are three main ways to backup your crypto wallet: a “seed freeze” (a mnemonic phrase consisting of between nine to twenty-four words), a wallet file backup (file formats include .dat, .json, and .bin), and the private key itself, which can be written on a piece of paper or saved in a text file.
The wallet that you are using should allow you the option of making a backup in any one of these formats. It may take a bit of poking around, but your wallet should allow you to create a backup. If you are using a wallet that does not allow you the option of backing up your private keys in some format, you may want to consider using a different wallet. The person that has the private keys controls the coins–end of story. If you don’t have access to your keys or the ability to make a backup, you may lose out in the end.
If possible, disconnect from the internet when you are creating your backup.
Storing Your Backup
You can store your backup (in any of these formats) on a USB drive or other kind of hard drive, or on a piece of paper (also known as a paper wallet). Any hardware that you use to store cryptocurrency should be encrypted. When you are storing your backup, try and be as offline as possible–disconnect from the internet before attempting to copy or move backup files.
The best strategy for storing your backup is to have multiple copies in multiple places. If your backups are stored in the same place as the original, you are much more vulnerable to losing everything. Spreading out your backups between several secure places is key.
Things to Remember
1. Use a wallet that allows you to create a backup.
2. Store multiple copies of your wallet in several secure places.
3. When creating and storing backups, keep your computer offline (if possible). Take extra security measures, like ensuring that your antivirus software is up-to-date and using an encrypted browser.
4. Never. Never, never! NEVER share your private keys with anyone. There is a multitude of scams on the internet that will ask you for your private keys for one reason or another. When you give away your private keys, you cannot get them back.



